Here we are again and I have to sadly say…..yet another OS (which I also love) that does not do what it promises. I know that you can do some major iptables kungfu under linux through command line, but when SuSE/Novell tries to sell you Yast as a graphical admin interface they should atleast check to make sure things are working properly.
Samba works under SuSE 10.x, and even with the firewall turned on the machine can act as a member of a Windows domain/workgroup. The problem though, is not with using Samba and having the firewall turned on. The problem is having Samba do more than just act as a member of the domain. We have a SuSE 10.1 machine that is part of our AD domain (spanning 3 subnets) and we also like it to be our local master and preferred master on the local subnet. It has one NIC active (ie: direct connection, with no NAT) and iptables firewall is active on that NIC. The problem is that the firewall rules that Yast2 creates are too restrictive (ie: if you just go to Yast2 and add Samba services as a allowed service).
Here is how you can fix this with a bit more effort:
- Setup the firewall with allowed services you like to punch through (ie: ssh, ftp and alike). Include Samba Server in the list as well under allowed services.
- Start the Firewall, at this point the basic samba stuff is working (ie: you can browse), but you more than likely can not do anything more in terms of domain participation.
- From the Yast2 interface go to System> /etc/sysconfig editor screen
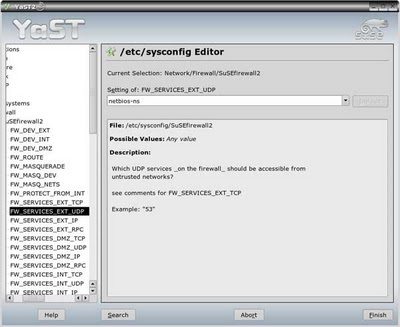
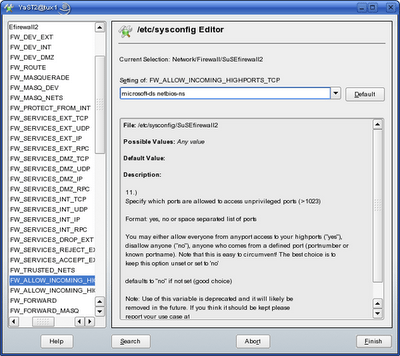
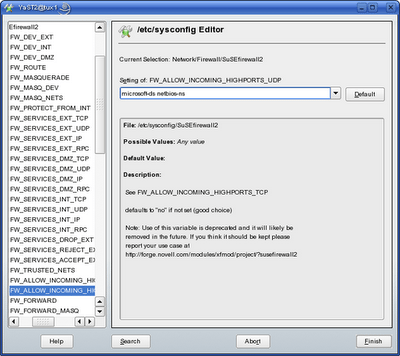
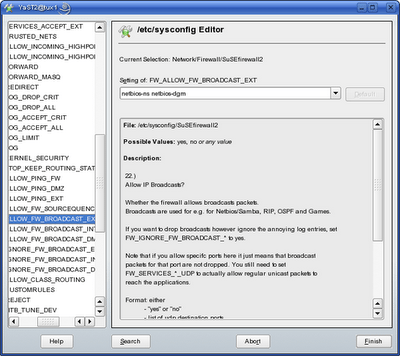
- Goto the section Network> Firewall> SuSEfirewall2
- ADD the following service names to appropriate sections ONLY if they are missing
- Under heading FW_SERVICES_EXT_TCP make sure you have the following:
microsoft-ds netbios-dgm netbios-ns netbios-ssn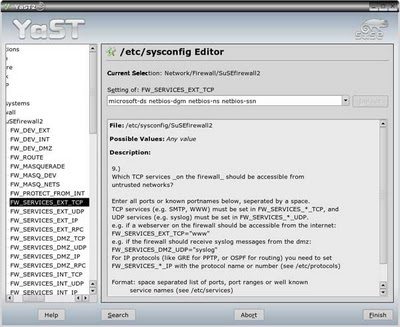
- Under heading FW_SERVICES_EXT_UDP make sure you have the following:
- Under heading FW_ALLOW_INCOMING_HIGHPORTS_TCP make sure you have the following:
- Under heading FW_ALLOW_INCOMING_HIGHPORTS_UDP make sure you have the following:
- Under heading FW_ALLOW_FW_BROADCAST_EXT make sure you have the following:
Now you’ve got the right holes punched through the firewall so click Finish and enjoy. You can now go back to the Samba config and make changes to become a serving member of your domain/workgroup.